Cyber security – Basic skills of an ethical hacker
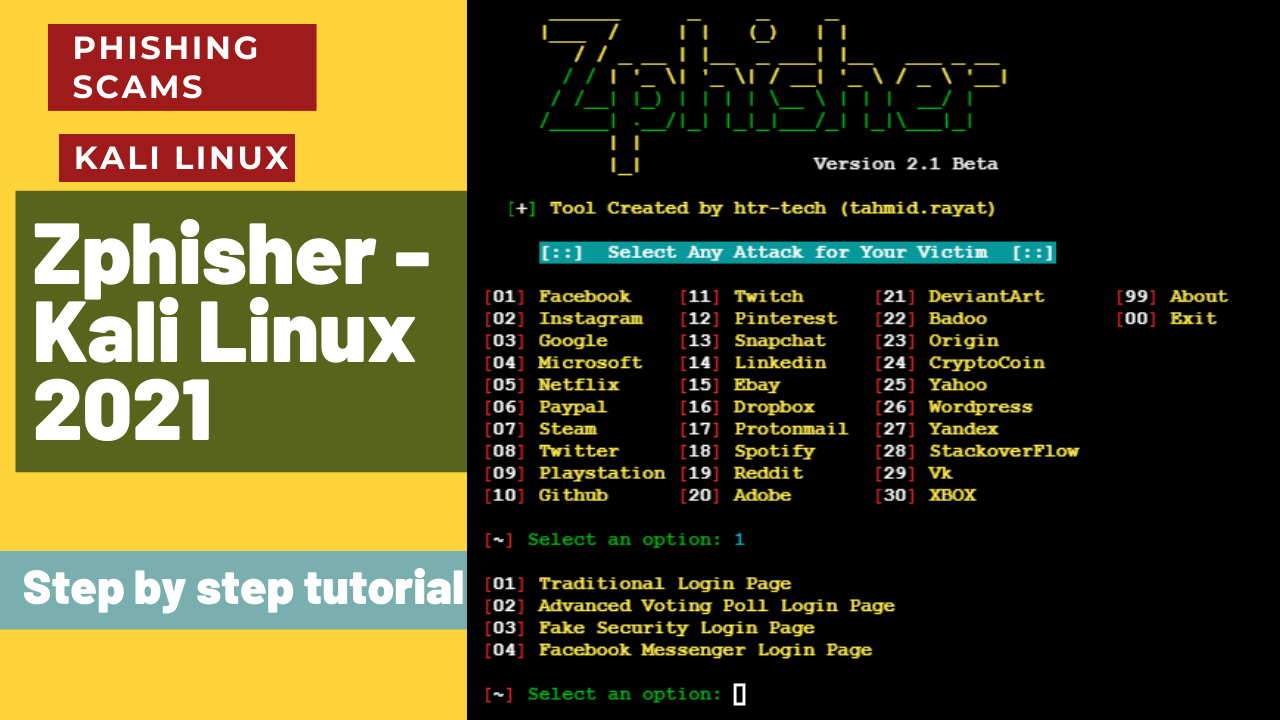
This educational video is tailored for students studying cybersecurity. It covers topics such as Nmap reconnaissance, brute force attacks with Hydra, Wi-Fi password cracking with WiFite, Metasploit exploitation, NTLM hash cracking, and DOS attacks, using tools on Kali Linux and Windows 7.